Liberate Your Company by Giving the End User Control of their Personal Data
The requirement of privacy laws such as GDPR, CCPA, and HIPAA put enormous burdens on company's that handle sensitive end user data.
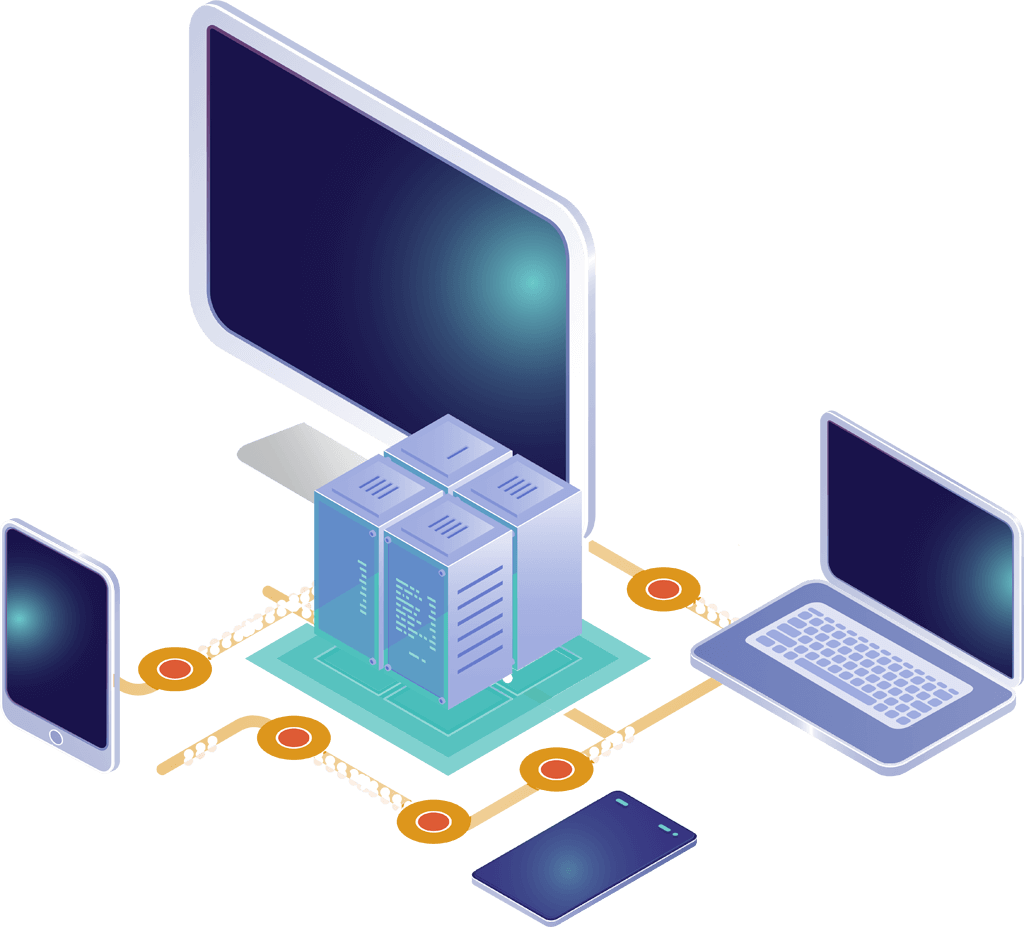
By leveraging Circle Secure Capsules, enterprises can give end users the power to secure and control their personal data on endpoint devices.
Now you can ensure compliance with ZERO overhead for complex and costly steps to track and then remove user's personal data.
Your application - and company - can never be the source of breach because you never have data in an unencrypted state - except when it is consumed by the end user on their own devices.