You do not need any application or installation whatsoever to try out Circle Access Lite. It uses HTML5 to store and manage cryptographic keys on your mobile phone for authentication.
You need the Circle Access Mobile App in order to leverage the on-device cryptographic capabilities of Circle Access Mobile and Digital Trust use cases.
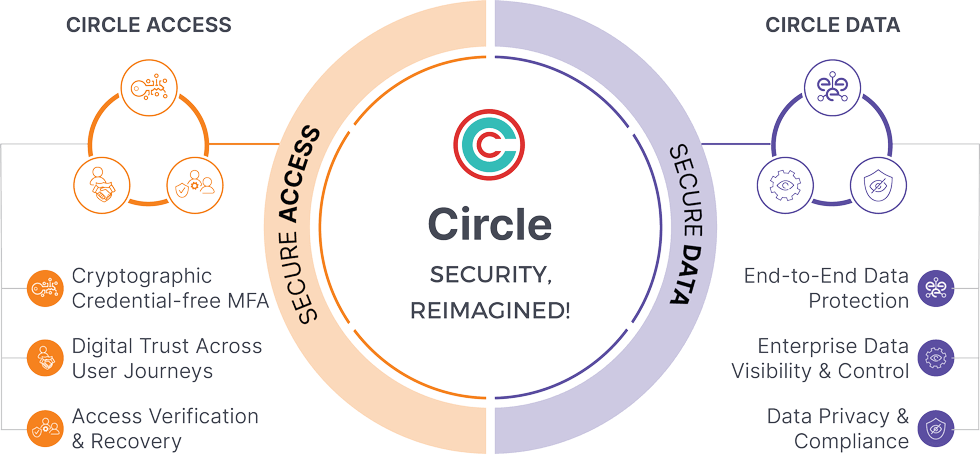
Note: Circle Access Mobile also includes Circle Service, so you gain all of the Data Protection, Privacy, and Control capabilities of Circle Data at the same time.
You need Circle Access Desktop:
This installs Circle Service to leverage its unique and powerful functionalities that run on the endpoint device.
In this demo, you can experience each frictionless UX one at a time. Or just try what you prefer.
In this simple demo, you can create a flow for approving payments from 3 people with separate weights for each.
The Circle Access Authorization APIs allow developers to create any authorization/approval workflow for a distributed workforce, with biometric verification of users and the option of cryptographic enforcement of actions granted.
This demo shows:
Circle Access Password Manager manages your passwords not on cloud but in a decentralized architecture by orchestrating the solution on device endpoints. The key differentiators of Circle Access Password Manager are
This demo illustrates key features of Circle Access Password Manager
Most encrypted emails system claim to be secure since they leverage an external key store to hold the keys that were used to encrypt and decrypt the email. The problem is, when the message needs to be displayed, the ‘server’ needs to ask the external key store for the decryption key; which means that while the server doesn’t store the key locally, it can still get it.
Go to our demo page for a video recording of integration with Microsoft Outlook along with code samples and explanations of how to implement it.
The demo illustrates two capabilities of Circle:
This is a video recording of integration with Microsoft Sharepoint. Click on the icon to play.
The demo illustrates the following areas of functionality.

