What is Circle Service?
Circle’s Service powers Circle's breakthrough Zero Trust, hybrid cloud + P2P security architecture to provide:
- Unrivaled data protection with device-based unbreakable AES 256 encryption and ZERO attack surface in the Cloud.
- Circle-of-Trust™ unspoofable Human-in-the-loop™ identity verification + authentication.
- Uncompromised privacy and data control - NOBODY but the data owner (whether that is the application developer or end user) can access their data - or metadata - EVER.
- Immutable data integrity and recovery with proprietary internal DLT.
Improve Your User Experience AND Security
Once you have integrated, end users just install Circle Service to enjoy credential-free authentication.

Users Install Circle Service
- Lightweight ultra-thin client.
- Browser plug-in UX.
- Install 1x and forget.
Users Authenticate
- DONE!
- No more passwords or credentials!
- Your device is your log-in, with user identity cryptographically bound to it.

Set Up a Circle-of-Trust
For Users and Customers that want advanced distributed unspoofable multi-factor human-in-the-loop™ identity verification + authentication.
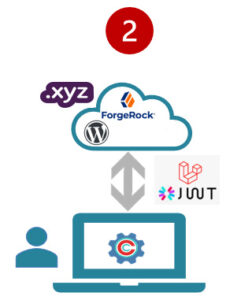
How Does Circle Service + API Work?
Our breakthrough hybrid P2P + Cloud architecture powers a new level of privacy, security and access control for developers
On the Endpoint Device
In the Cloud
Circle Service
Lightweight Thin Client - install & forget
- AES 256 Encryption
- Key Management
- Invite + Authentication
- Circle Secure Capsules

Keys Bound to the Device
- Bound to device keychain / Trusted Platform Module (TPM)
Circle Secure Capsules
AES 256 encrypted containers for anything - files, databases, structure & unstructured data

A CircleCan contain any number of Open or Locked capsules

Open:
accessible with the master capsule key

Locked:
separately encrypted with unique key
Circle Web Services
Hybrid P2P
- AES 256 Encryption
- Key Management
- Invite + Authentication
- Circle Secure Capsules

Circle Server has copies – in data blobs – of each private secure capsule, but no keys. Zero ability to open them or even know what they are
App Web Services

Developers can host and white label Circle Service on their servers for End Users to install

Large developers can host data blobs & Web services on private cloud or on- prem if desired
